by Rowan Report | Jan 23, 2026 | Artificial Intelligence
Purpose-Built AI for Care at Home
Architecture, Scalability, and Security
In part one of this 4-part series, we discussed how care at home agencies can realize the full impact of AI software that goes beyond the testing period. The best way to do this is to find purpose-built tech and evaluate AI solutions for real-world outcomes.
Part two focuses on AI architecture, scalability and security.
Architecture and Scalability Across the Tech Ecosystem
AI does not operate in isolation. It sits within a broader ecosystem of EHRs, compliance programs, quality initiatives, and IT infrastructure.
For care-at-home organizations, long-term outcomes depend on whether an AI platform can:
- Adapt to evolving documentation and regulatory requirements
- Scale reliably during census fluctuations
- Integrate cleanly with existing systems
- Improve over time without creating operational drag
Health informatics research increasingly highlights risks such as model drift — where AI performance degrades as populations, workflows, or clinical practices change — reinforcing the need for continuous monitoring rather than one-time deployment.
Vendors with limited clinical depth or brittle configurations may show early promise in pilots, but often struggle to sustain efficiency and ROI at scale.
and the Link to Long-Term Value
HIPAA compliance remains foundational, but AI introduces additional governance considerations related to transparency, accountability, fairness, and ongoing risk management.
Healthcare organizations increasingly evaluate AI vendors based on:
- Independent security and privacy assessments
- Clear contractual boundaries around data use
- Explicit retention and deletion policies
- Documented processes for monitoring AI behavior over time
Recent federal regulation, including the ONC’s HTI-1 Final Rule, formalizes new transparency and risk-management expectations for AI-enabled clinical systems — extending well beyond traditional privacy frameworks.
Emerging standards such as ISO 42001, focused on AI management systems, reflect a broader shift toward formal governance of AI in high-risk domains like healthcare. While adoption is still evolving, these frameworks provide executives with a useful lens for assessing vendor maturity.
Strong governance is not only a risk-mitigation strategy — it is a prerequisite for sustaining outcomes, protecting organizational reputation, and maintaining provider trust.
AI has demonstrated the potential to reduce administrative burden, improve documentation quality, and deliver measurable ROI in healthcare — including regulated, care at home settings.
However, results are not guaranteed. They depend on evidence-backed design, workflow alignment, scalability, and governance discipline.
For care-at-home leaders, the most reliable path to value is not adopting AI quickly, but evaluating it rigorously — with a focus on how the technology is built, validated, and governed.
For organizations navigating pilot fatigue, the critical shift is not testing more tools, but selecting platforms designed for scale, governance, and long-term operational impact.
This is part 2 of a 4-part series. Read part 1 and come back next week for part 3, “From Evaluation to Execution.”
At Eleos, we believe the path to better healthcare is paved with provider-focused technology. Our purpose-built AI platform streamlines documentation, simplifies compliance and surfaces deep care insights to drive better client outcomes. Created using real-world care sessions and fine-tuned by our in-house clinical experts, our AI tools are scientifically proven to reduce documentation time by more than 70% and boost client engagement by 2x. With Eleos, providers are free to focus less on administrative tasks and more on what got them into this field in the first place: caring for their clients.
©2026 by The Rowan Report, Peoria, AZ. All rights reserved. This article originally appeared in The Rowan Report. One copy may be printed for personal use: further reproduction by permission only. editor@therowanreport.com
by Rowan Report | Jan 9, 2025 | CMS, Partner News, Regulatory
HHS OCR Proposes Updates to the HIPAA Security Rule to Respond to Emerging Threats
by Paul F. Schmeltzer and John F. Howard, Clark Hill PLC
On Dec. 27, the Department of Health and Human Services (HHS) issued proposed updates to the HIPAA Security Rule to address evolving cybersecurity threats in healthcare. Introduced through a Notice of Proposed Rulemaking (NPRM) by the Office for Civil Rights (OCR), the substantial updates aim to enhance the protection of electronic protected health information (ePHI) while aligning the two-decade-old regulations with current technological advancements. These changes are especially crucial in a healthcare environment increasingly reliant on electronic health records (EHRs), online patient portals, telehealth platforms, and interconnected medical devices.
Since its adoption in 2003, the HIPAA Security Rule has served as the foundation for safeguarding ePHI. However, the healthcare landscape has changed dramatically with the rise of cyber threats like ransomware, phishing attacks, and hacking incidents that result in data breaches. OCR’s investigations into HIPAA compliance across the healthcare industry have also revealed significant inconsistencies, underscoring the need for updated regulations that provide clarity and enforceability.
Revisiting “Addressable” vs. “Required” Specifications
Among the most significant aspects of the proposed changes in the NPRM is the reconsideration of the distinction between “required” and “addressable” implementation specifications, a hallmark of the original Security Rule that has often caused confusion. Required specifications must be implemented as outlined, with no exceptions. Addressable specifications, on the other hand, give entities the flexibility to evaluate their feasibility and adopt alternative measures if implementing the original specification is deemed unreasonable or inappropriate. This flexibility has often been relied on by mid and small-sized HIPAA-covered entities in their compliance efforts.
The NPRM proposes eliminating the concept of “addressable” implementation specifications and making all implementation specifications required, with limited exceptions. This includes reclassifying encryption of ePHI at rest and in transit as a required specification, reflecting its essential role in mitigating cyber risks and its widespread availability. Previously, entities could justify not using encryption if they documented their rationale and implemented alternative measures. The proposed change eliminates this flexibility, simplifying compliance expectations and reinforcing encryption as a baseline safeguard for ePHI. This same change would follow for other specifications under the rule, highlighting OCR’s desire to strengthen and simplify the Security Rule.
Strengthened Administrative Safeguards
The NPRM introduces several enhancements to administrative safeguards to address modern security risks. Comprehensive risk analysis remains a cornerstone of HIPAA compliance, but the proposed updates add specificity to these requirements. Entities will be required to maintain a detailed inventory of all technology assets that interact with ePHI and map how ePHI flows within their systems. This mapping ensures visibility into where sensitive data resides and how it is accessed, helping organizations proactively identify and address vulnerabilities. The inventory and map would then be required to be reviewed every 12 months as part of an entity’s risk assessment and risk management processes.
Incident response planning is also emphasized. Entities must develop robust written plans that include protocols for detecting, containing, and recovering from cyberattacks or breaches. These plans should be regularly updated to align with emerging threats and best practices. Workforce training requirements are also expanded under the NPRM, with a focus on providing comprehensive and role-specific education. These programs must address unique vulnerabilities tied to specific job functions and be updated regularly to combat threats like phishing and social engineering.
Strengthened Physical and Technical Safeguards
Physical and technical safeguards also receive significant attention in the NPRM. To secure ePHI, physical access to facilities and devices must be tightly controlled through advanced measures such as biometric authentication, badge systems, and video surveillance. These controls aim to protect ePHI from unauthorized access, theft, or tampering.
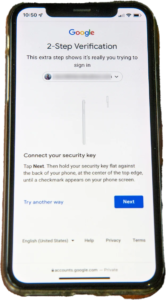
The NPRM proposes a definition of the term “multi-factor authentication” (MFA) that entities would be required to apply when implementing the proposed rule’s specific requirements for authenticating users’ identities through verification of at least two of three categories of factors of information about the user, such as passwords combined with biometrics, to secure access to systems containing ePHI. Additionally, the NPRM encourages using advanced threat detection tools like intrusion detection systems, AI-powered anomaly detection, and real-time breach alerts to proactively address security risks.
Addressing Challenges for Small and Rural Providers
HHS recognizes the unique challenges faced by smaller healthcare providers, particularly those in rural and tribal areas, where resources for implementing complex security measures are often limited. The NPRM seeks to provide scalability, allowing entities to implement solutions proportional to their size and complexity. Tailored guidance and tools are expected to support these providers, and regional collaborations are encouraged to pool resources and expertise for improved cybersecurity.
Implications for Stakeholders
For healthcare providers and business associates, the proposed updates necessitate significant investment in technology, training, and compliance infrastructure. Allocating budgets for tools like encryption and MFA, revising and drafting policies and procedures, and updating vendor contracts to ensure alignment with new standards are critical steps. Failure to comply with these updated requirements could lead to stricter enforcement actions and penalties. Fortunately, the proposed changes also remove some of the guesswork needed to comply with the Security Rule. Making areas where investment is needed easier to identify.
Patients stand to benefit significantly from the proposed changes, as stronger protections for sensitive health information can help rebuild trust in healthcare systems. By reducing the frequency and severity of breaches, the NPRM supports greater patient engagement and the adoption of digital health technologies. Regulators, equipped with clearer enforcement guidelines, will be better positioned to ensure compliance and address violations effectively.
Alignment with Broader Cybersecurity Efforts
The proposed updates align with national and international cybersecurity frameworks, including the NIST Cybersecurity Framework and the General Data Protection Regulation (GDPR). These alignments position the U.S. healthcare sector as a global leader in data security while promoting best practices like continuous monitoring, risk management, and strong encryption.
Implementation Timeline and Next Steps
The NPRM is to be published in the Federal Register on Jan. 6, 2025, after which a 60-day public comment period will follow. The final rule will take effect 60 days post-publication. Entities will have 180 days to achieve compliance, with additional time provided to update business associate agreements. The NPRM encourages stakeholders to provide feedback on the practicality and cost-effectiveness of the proposed changes during the comment period.
Conclusion: A Necessary Evolution in Cybersecurity
The proposed updates to the HIPAA Security Rule represent a critical step forward in securing ePHI against today’s sophisticated cyber threats. By reclassifying key specifications, enhancing safeguards, and providing greater clarity for compliance, the NPRM builds a robust framework for protecting both patients and providers. While these changes may pose challenges for some organizations, they are an essential evolution in safeguarding sensitive data in an increasingly digital world. As healthcare continues its digital transformation, these updates underscore the importance of cybersecurity as a cornerstone of quality care and public trust. Investment in a strong cybersecurity posture up front will prove valuable and ultimately save the entire healthcare industry in the long run.
This publication is intended for general informational purposes only and does not constitute legal advice or a solicitation to provide legal services. The information in this publication is not intended to create, and receipt of it does not constitute, a lawyer-client relationship. Readers should not act upon this information without seeking professional legal counsel. The views and opinions expressed herein represent those of the individual author only and are not necessarily the views of Clark Hill PLC. Although we attempt to ensure that postings on our website are complete, accurate, and up to date, we assume no responsibility for their completeness, accuracy, or timeliness.
©2025 This article originally appeared on the Clark Hill website and is reprinted with permission.
by Tim Rowan | May 2, 2024 | Admin, Privacy and Security, Regulatory, Telehealth
by Tim Rowan, Editor Emeritus
You know the routine. Everyone does. You log into your bank, airline account, or health insurance web portal, enter the correct password, and are directed to look on your smartphone 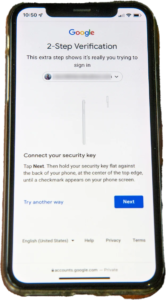 for a code to enter to fully authorize your login. The name for this is Multi-Factor Authentication, or MFA. Lack of MFA procedures leaves your company at risk, which UnitedHealth discovered when it was grilled by Congress about the cyberattack on Change Healthcare.
for a code to enter to fully authorize your login. The name for this is Multi-Factor Authentication, or MFA. Lack of MFA procedures leaves your company at risk, which UnitedHealth discovered when it was grilled by Congress about the cyberattack on Change Healthcare.
United Health Grilled by Congress
In his testimony to the House Energy and Commerce Committee Wednesday, UnitedHealth Group CEO Andrew Witty blamed the absence of MFA as the weak link that allowed a ransomware attack to cripple subsidiary Change Healthcare in February. The breach had ripple effects throughout healthcare, given Change’s role as fiscal intermediary for thousands of providers. Healthcare systems on every level were unable to file claims and receive payments.
Asked by the committee why Change Healthcare, which United acquired in late 2022, did not have MFA in place, Witty testified, “Change Healthcare was a relatively older company with older technologies, which we had been working to upgrade since the acquisition. But for some reason, which we continue to investigate, this particular server did not have MFA on it.”
CBS News reported that Change Healthcare processes 15 billion transactions a year. “The scale of the attack,” their report stated, “meant that even patients who weren’t customers of UnitedHealth were potentially affected. Personal information that could cover a ‘substantial portion of people in America’ may have been taken in the attack.” The breach has already cost UnitedHealth Group nearly $900 million, plus the $22 million ransom Witty decided to pay to the hackers.
The Russia-based ransomware gang, ALPHV, or “BlackCat,” claimed responsibility for the attack, bragging that it stole more than six terabytes of data, including “sensitive” medical records. The attack triggered a disruption of payment and claims processing around the country.
We followed up our initial report on the attack with CMS guidance on March 20, 2024 and an update on April 11, 2024, with reports that Change Healthcare was being blackmailed again by another ransomware gang, RansomHub, who claimed to have 4TB of data from Change Healthcare and demanded another ransom payment.
Walmart & Optum, UnitedHealth Trouble Spots?
UnitedHealth Group is also in headline news this week for two other reasons. The company’s Optum division, which owns home care giant CenterWell, formerly Kindred at Home, and which is awaiting government approval for its bid to acquire Amedisys, has quietly been executing a reduction in force. Reports are that the bulk of the layoffs are hitting “Optum Virtual Care,” the name given to naviHealth following its $1 billion acquisition in 2020. Following a surge in demand during the pandemic, the company is apparently abandoning telehealth services.
formerly Kindred at Home, and which is awaiting government approval for its bid to acquire Amedisys, has quietly been executing a reduction in force. Reports are that the bulk of the layoffs are hitting “Optum Virtual Care,” the name given to naviHealth following its $1 billion acquisition in 2020. Following a surge in demand during the pandemic, the company is apparently abandoning telehealth services.
A planned 10-year collaboration between UnitedHealth and Walmart to provide virtual healthcare services ended Tuesday after only one year. On April 30, the retail giant announced that it will close its 51 health centers across five states due to the “challenging reimbursement environment” and rising operating costs, which have resulted in a lack of profitability. Like Optum Virtual Care, the centers were providing virtual services via telehealth.
A sign of the post-pandemic times? Perhaps. We will keep watching.
 Tim Rowan is a 30-year home care technology consultant who co-founded and served as Editor and principal writer of this publication for 25 years. He continues to occasionally contribute news and analysis articles under The Rowan Report’s new ownership. He also continues to work part-time as a Home Care recruiting and retention consultant. More information: RowanResources.com
Tim Rowan is a 30-year home care technology consultant who co-founded and served as Editor and principal writer of this publication for 25 years. He continues to occasionally contribute news and analysis articles under The Rowan Report’s new ownership. He also continues to work part-time as a Home Care recruiting and retention consultant. More information: RowanResources.com
Tim@RowanResources.com
©2024 by The Rowan Report, Peoria, AZ. All rights reserved. This article originally appeared in Healthcare at Home: The Rowan Report.homecaretechreport.com One copy may be printed for personal use: further reproduction by permission only. editor@homecaretechreport.com


 for a code to enter to fully authorize your login. The name for this is Multi-Factor Authentication, or MFA. Lack of MFA procedures leaves your company at risk, which UnitedHealth discovered when it was grilled by Congress about the cyberattack on Change Healthcare.
for a code to enter to fully authorize your login. The name for this is Multi-Factor Authentication, or MFA. Lack of MFA procedures leaves your company at risk, which UnitedHealth discovered when it was grilled by Congress about the cyberattack on Change Healthcare. formerly Kindred at Home, and which is awaiting government approval for its bid to acquire Amedisys, has quietly been executing a reduction in force. Reports are that the bulk of the layoffs are hitting “Optum Virtual Care,” the name given to naviHealth following its $1 billion acquisition in 2020. Following a surge in demand during the pandemic, the company is apparently abandoning telehealth services.
formerly Kindred at Home, and which is awaiting government approval for its bid to acquire Amedisys, has quietly been executing a reduction in force. Reports are that the bulk of the layoffs are hitting “Optum Virtual Care,” the name given to naviHealth following its $1 billion acquisition in 2020. Following a surge in demand during the pandemic, the company is apparently abandoning telehealth services. Tim Rowan is a 30-year home care technology consultant who co-founded and served as Editor and principal writer of this publication for 25 years. He continues to occasionally contribute news and analysis articles under The Rowan Report’s new ownership. He also continues to work part-time as a Home Care recruiting and retention consultant. More information:
Tim Rowan is a 30-year home care technology consultant who co-founded and served as Editor and principal writer of this publication for 25 years. He continues to occasionally contribute news and analysis articles under The Rowan Report’s new ownership. He also continues to work part-time as a Home Care recruiting and retention consultant. More information: